Our three lines of defence
Over the past 17 years we have deployed a self-owned low-latency network inside our datacentre creating the best DDoS Protection for our Customers. It has been so successful that Corero our DDoS Appliance vendor created a representative Case Study together with us, for the whole gaming industry. https://www.corero.com/blog/case-study-ociris
We are able to create individual rules, filters, and patterns for every single service we provide and we are adding many more every day. Our NOC reviews in detail every single attack and checks in-game if there are any ongoing attacks, which may be causing harm to the game experience: checking for evidence of any rubber-banding or disconnect for players etc.
Once detected we can adjust rules until the attack has little to no impact on the players. The experience that we have gained throughout the years, has essentially made us experts in DDoS protection and UDP based Gaming Packet Processing.
The fact that we are in full control of every single part of our network in every location; grants us the ability to adjust every single facet of the game that we are hosting. With our broad knowledge of gaming, engines and network traffic; we are able to detect anomalies fast and create appropriate counter measures.
At GPORTAL, we understand that gaming networks are highly individual, however two factors are always the same: bandwidth and latency. Our approach to accommodate this is relatively straightforward – firstly we arrange for as many end-consumers to be directly connected to the infrastructure, nearby to each point of presence (POP) in major cities and states.
However, this method can be expensive and so we have developed a separate approach, where we utilise many network hosts to aide information workloads. Currently we use both approaches, dependant on network requirements; we also strive to improve this infrastructure day by day.
Network POPs – First line of defence
With so many self-managed POPs all around the globe we made an important step toward, enabling us to keep our entire network clean and stable. With network POP’s and Layer2 interconnections between them and the major locations where the compute nodes reside in and serve studios and developers, you gain the option to mitigate traffic where it origins instead of moving all packets like in a funnel towards the attacked IP in one spot – you can reduce the malicious bandwidth upfront at many spots.
The most important part for this First Defence Line, are the ACL’s that are in place on GPORTALs own routers and in front directly at the upstream carrier. So, we can be sure that bandwidth won’t be saturated at any point.
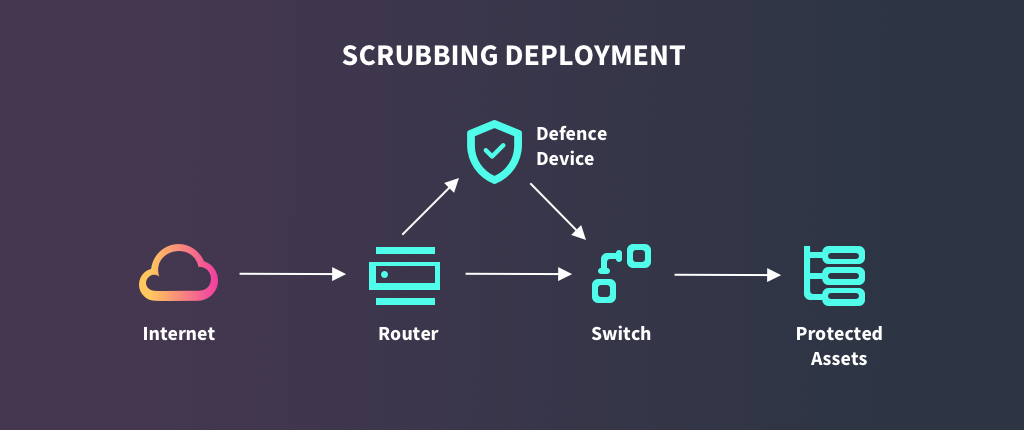
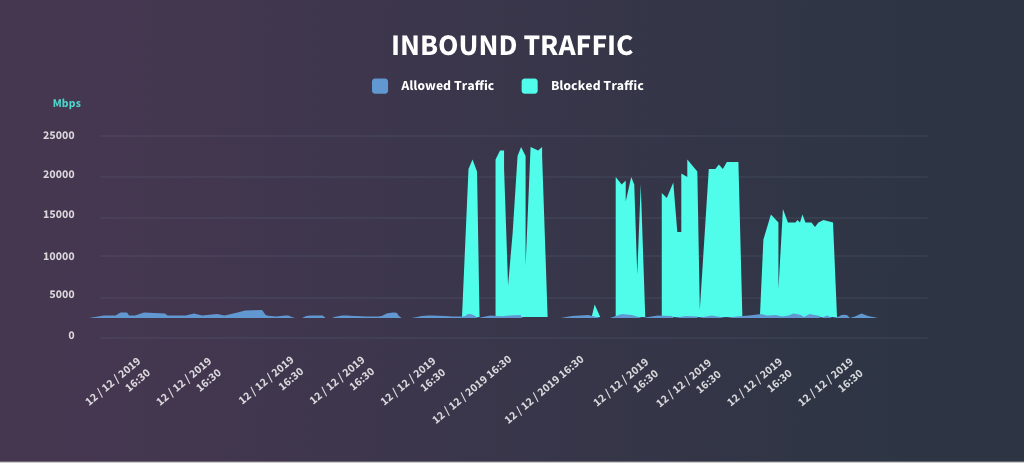
The second thing, that needs to be implemented at POP’s or Major locations where exchange between our network and the upstream carriers is a scrubbing system. A scrubbing system is a non inline smart way to mitigate DDoS traffic. In terms of an Attack, a system will detect a traffic anomaly and will reroute with a next-hop route injection the affected IP address towards a scrubbing system. And the result means that the main uplink will have clean traffic most of the time.
Secondly the malicious traffic can be mitigated by the Corero which allows us to have smarter filters in place that can also block by payload and other patterns which a normal ACL wouldn’t be capable of. The filtered traffic will be forward to its destination. The attack server shouldn’t notice any impact and the player shouldn’t either.
Second line of defence
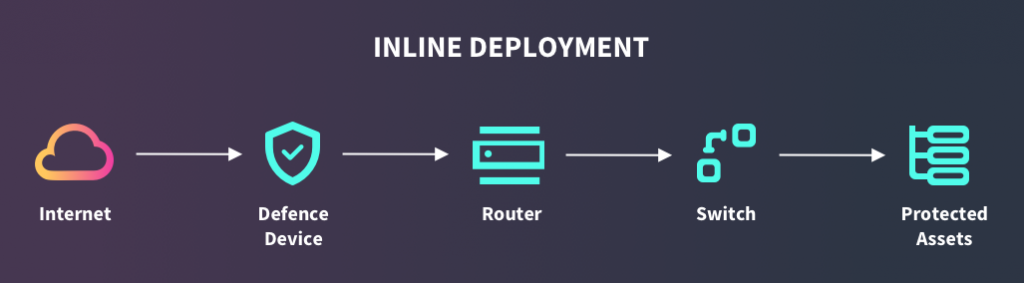
The second defence Line is the inline mitigation with a higher bandwidth directly at major locations. Once will have the routers and your upstream carriers in place we limit the bandwidth of an attack, to not saturate your overall existing bandwidth. Additionally, we will add an inline approach to mitigate traffic. This exists for one reason.
All packets will flow through the Corero, can be analysed and immediately mitigated the fastest way available. In-Line Mitigation makes sense, because some fragile gameservers may have a negative impact while switching traffic to a out of band scrubbing system. We have scrubbing systems available at our POP’s as decribed in our First Line of defence section.
Third line of defence
A game has certain stages where it needs access to different areas inside our network, for example when starting a game launcher, it would need access to user authentication, shop, different content, maybe chat etc., so the idea is to restrict this access coming from this user to those areas, and to limit his traffic for normal usage.
After starting the actual game, we widen the area of access and like masterserver to retrieve the serverlist, lobby system to start a match with other players, and last the dedicated server itself where the player wants to play the game.
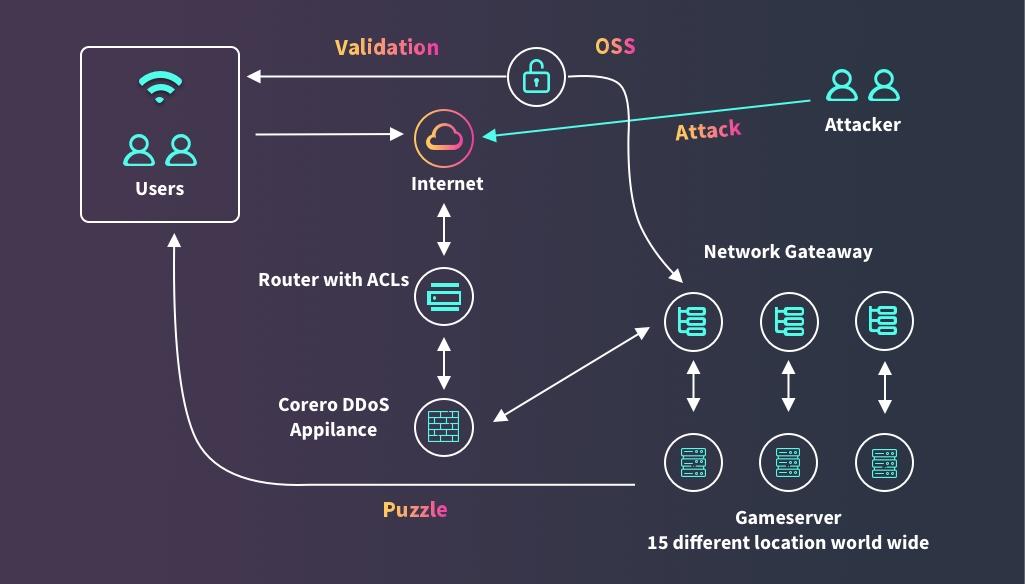
As soon as the game starts the implemented SDK would send IP:PORT and Steam ID64, EGS ID or Profile name, to our worldwide available Endpoints. That will lead the client to gain access to different areas of services.
- Masterserver to retrieve the Serverlist
- Lobby System to start a Match
- Offloading Banlists to disallow right from the start any traffic from a former banned user to reach any service
- Friendliest, Chat, in game Shops based on the used Online Subsystem eg. Steam or Epic Game Store
After the user selected a server to join or started a match and got redirected to an actual gameserver, the server will perform a puzzle to generate a unique pair of keys to validate each network packet towards the server. A Fingerprint put inside the header of each UDP packet, ensures that no spoofed IP of any validated client will trick our infrastructure.
All Data are stored in a lightning fast cache which interact with our self-developed network gateway at each location. For scaling and redundancy those network gateway come in a huge cluster talking iBGP with ECMP in order to load balance traffic among them. BFD will make sure that any link-failure will be detected in less a millisecond and the packets get thanks to iBGP routed into our EVPN + VxLAN multi-tenant Network infrastructure.
There is no need for a big hassle to interact with our engineers to implement this solution. An SDK for all major engines out there and a simple API Key is all you need to make this work.
This solution makes sure, that only valid players, with a valid profile or gamekey are able to talk inside the thresholds of our existing DDoS Application and ACL’s provided upfront. All other packets get blocked on our self-developed network gateway. Handshakes, Puzzle and Fingerprints make sure that all packets arriving at different areas of our Network are valid.
Out control panel leverage you to check current statistic, graphs, and also allows you to whitelist source-ips for other services such as Live-Ops etc.